Digital Forensics
Have you suffered a data breach, loss of information or been subjected to unauthorized extraction of sensitive data? Do you suspect that an employee or a third party has copied sensitive data? Regardless of root cause or incident, you will get the best forensic help from our certified forensic specialists.
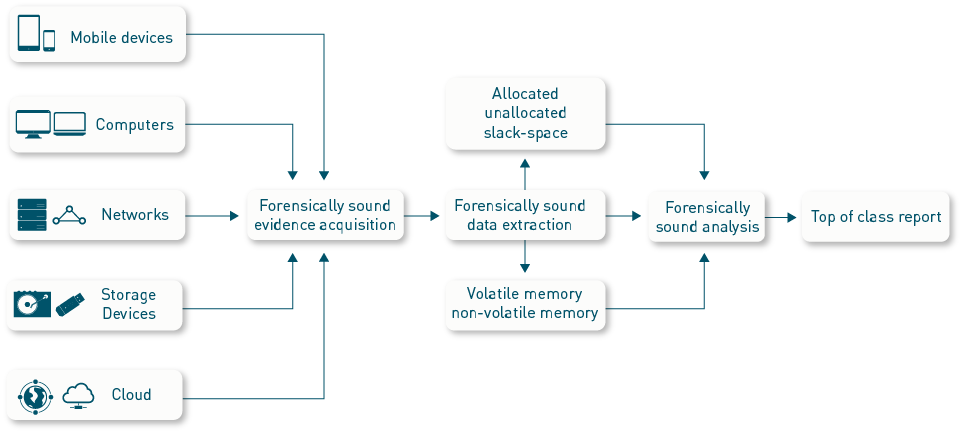
We acquire evidence, extract both volatile/non-volatile data and perform the analysis according to the best forensic principles and standards, so that you can go to court if needed – with our report in your hand.
Our forensic specialists work with:
- Mobile devices (iPhone, Android, Tablets)
- Computers (Laptops, PC, Mac)
- Networks (server and infrastructure memory analysis, log acquisition, log analysis)
- Storage devices (UMS, USB, disks, NVMe)
- Cloud environments
What you get:
- A digital forensics investigation, which is based on forensically sound methodology and meticulous attention to detail
- Answers to your questions regarding the chain of events – likely timeline and culprits
- Data loss recovery (where applicable)
Contact us today!